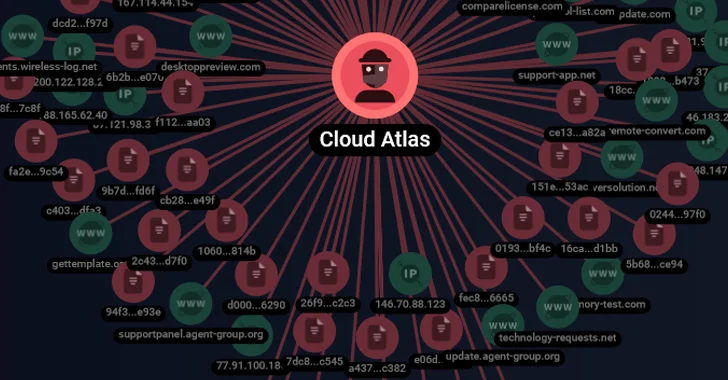
Threat actors are called Cloud Atlas Related to a series of spear phishing attacks targeting Russian businesses.
According to a report by FACCT, an independent cybersecurity company established after Group-IB officially exited Russia earlier this year, targets included a Russian agro-industrial enterprise and a state-owned research company.
Cloud Atlas is a cyber espionage group of unknown origin that has been active since at least 2014. This threat actor, also known as Clean Ursa, Inception, Oxygen, and Red October, is known for its ongoing activities targeting Russia, Belarus, Azerbaijan, Turkey, and Slovenia.
In December 2022, Check Point and Positive Technologies detailed a multi-stage attack sequence that resulted in the deployment of a PowerShell-based backdoor, known as PowerShower, and a DLL payload capable of communicating with an attacker-controlled server.
From user to administrator: Learn how hackers gain total control
Learn the secret tactics hackers use to become administrators, and how to detect and stop it before it’s too late. Register now for our webinar.
Join now
The starting point is a phishing message with a bait file that exploits CVE-2017-11882, a six-year-old memory corruption flaw in the Microsoft Office Equation Editor, to initiate the execution of a malicious payload, which Cloud Atlas employs Technology back in October 2018.

“The attacker’s large-scale spear phishing campaign continues to use its simple but effective methods to compromise its targets,” Kaspersky noted in August 2019. “Unlike many other intrusion sets, Cloud Atlas is There was no option to use open source implants during the attack.” Recent activities to reduce discrimination. “
The latest kill chain described by FACCT is similar to the one described by Positive Technologies, which successfully exploited CVE-2017-11882 via RTF template injection, paving the way for shellcode responsible for downloading and running obfuscated HTA files. The emails came from popular Russian email services Yandex Mail and VK’s Mail.ru.
The malicious HTML application then launches Visual Basic Script (VBS) files, which are ultimately responsible for retrieving and executing unknown VBS code from the remote server.

“The Cloud Atlas group has been active for years and has carefully considered all aspects of its attacks,” Positive Technologies said of the group last year.
“The group’s toolkit has not changed in years – they attempt to hide malware from researchers by requesting disposable payloads and validating them. The group avoids this by using legitimate cloud storage and well-documented software capabilities. Network and file attack detection tools, especially in Microsoft Office.”
The company says at least 20 Russia-based organizations have been compromised by Decoy Dog, a modified version of the Pupy RAT, which it attributes to an advanced persistent threat actor known as Hellhounds.
In addition to allowing attackers to remotely control infected hosts, this actively maintained malware also comes with a script designed to transmit telemetry data to a user named “Lamir Hasabat” (@lahat) on a Mindly.Social instance on Mastodon. “Automatic” account.
Security researchers Stanislav Pyzhov and Aleksandr Grigorian said: “After the release of information about the first version of the decoy dog, malware authors spent a lot of effort Efforts to hinder its detection and analysis in traffic and file systems.”