Thread hijacking attack. This happens when someone you know has their email account compromised, and you’re suddenly caught up in an existing conversation between the sender and someone else. The letters exploit recipients’ natural curiosity to be copied in private discussions and are modified to contain malicious links or attachments. This is the story of a recent threadjacking attack, in which a reporter was plagiarized from a phishing email from an unwilling subject who had a recent scoop.
September 2023, Pennsylvania News Media lancaster online website posted about Adam Kiddana wealthy businessman with a criminal record, is a major donor to Republican causes and candidates, including Rep. Lloyd Smucker (R-Pa).
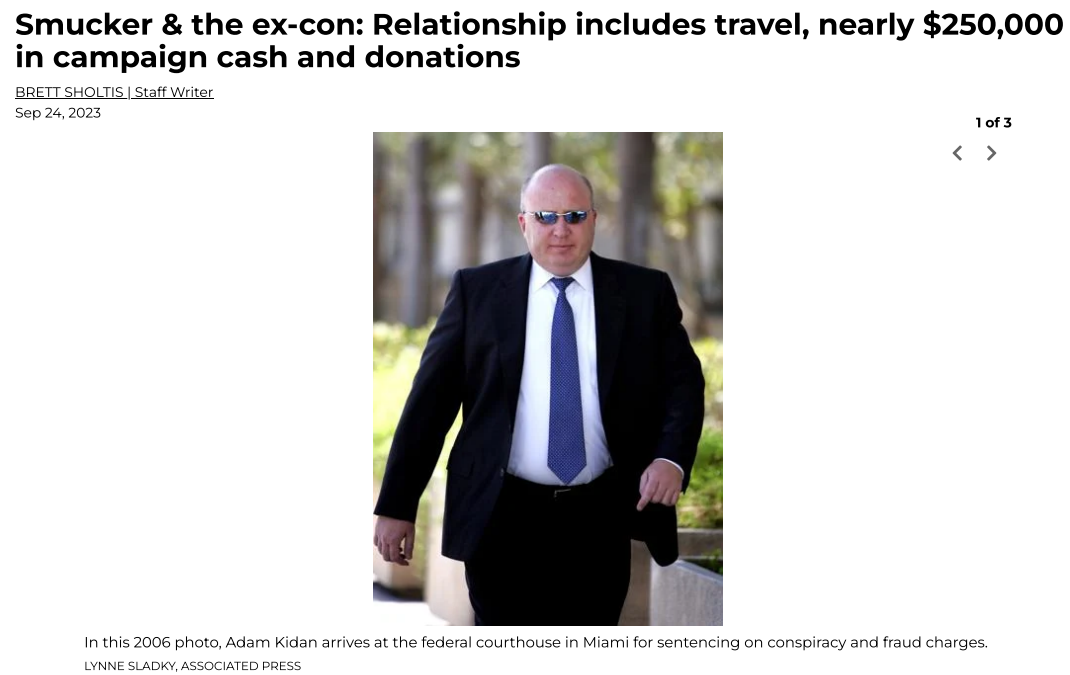
Lancaster Online’s story about Adam Kidan.
A few months after this article was published, the story’s author Brett Shortis Received two emails from Kidan, both containing attachments. One of the messages appeared to be a lengthy conversation between Kidan and a colleague, with the subject line “Reply: Data sent successfully.” The second letter was a shorter email from Kidan, with the subject line “Confirm New Work Order” and the message content was simply: “Please look for attachments.”
Shortis said he clicked on an attachment in one of the emails, which then launched a web page that looked exactly like the Microsoft Office 365 login page. Analysis of the web page shows that it checks any credentials submitted on the real Microsoft website and returns an error if the user enters false account information. A successful login will log the submitted credentials and forward the victim to the real Microsoft website.
But Shortis said he did not enter his Outlook username and password. Instead, he forwarded the messages to LancasterOneline’s IT team, who quickly flagged them as phishing attempts.
lancaster online Executive Editor Tom Moores Mr. Kidan said the two phishing messages from Mr. Kidan caught the newsroom’s attention because Kidan had repeatedly threatened to sue the news outlet over Shortis’ story.
“We’re just confused,” Moores said. “This appears to be a phishing attempt, but we are confused as to why it is coming from a well-known businessman we have written about. Our initial reaction is confusion, but other than sending it to the FBI, we have no idea What else can be done.”
The thread from Mr. Kidan hijacked the phishing bait included in the email.
Kiddan was sentenced to 70 months in federal prison in 2006 after pleading guilty, along with disgraced lobbyist Jack Abramoff, to defrauding lenders. Jack Abramoff’s corruption has become emblematic of Washington’s over-the-top influence peddling. He was paroled in 2009 and in 2014 his family moved to a home in Lancaster County, Pennsylvania.
The FBI has not yet responded to LancasterOnline’s report. KrebsOnSecurity Messages sent to Kidan’s email address have bounced and been blocked. Messages left for Mr. Kidan’s company, Empire Workforce Solutions, were not returned.
There is no doubt that the FBI saw the emails from Kidan, most likely because Mr. Kidan’s Microsoft Outlook account was compromised and used to send malicious emails to people on his contact list.
Thread hijacking attacks are not new, but that’s mainly because many web users still don’t know how to recognize them.email security company proof point It said it has tracked more than 90 million malicious messages using this attack method in the past five years.
A key reason why thread hijacking is so successful is that these attacks typically do not include the message that gives away most phishing scams: a fabricated sense of urgency. Most phishing threats will warn you that if you don’t act quickly, there may be negative consequences, such as account suspension or unauthorized high charges.
In contrast, thread hijacking campaigns tend to patiently exploit the recipient’s natural curiosity.
Ryan KalumberProofpoint’s chief strategist said the most common examples of thread hijacking may be “CEO scams” or “business email compromise” scams, in which employees are tricked by emails from high-level executives into sending millions of dollars to overseas fraudsters. .
But Kalumber said these low-tech attacks are still very effective because they tend to catch people off guard.
“It works because you feel like you’re suddenly involved in an important conversation,” Kalumber said. “When people start reading it, it feels very different because you think you’re observing a private conversation between two different people.”
Some thread hijacking attacks actually involve multiple threat actors actively talking while copying (but not addressing) recipients.
“We call these multi-person phishing scams, and they are often combined with thread hijacking,” Kalumber said. “It’s basically a way to build more rapport rather than just copying someone else’s message in an email. The longer the conversation goes on, the more successful they seem to be because some people start replying to the post [and participating] Psychosocial aspects. “
The best advice for avoiding phishing scams is to avoid clicking on unauthorized links or attachments in emails, text messages, and other media. If you’re not sure whether the message is legitimate, take a deep breath and manually visit the website or service in question – ideally, using a browser bookmark to avoid potentially mistaken sites.
